A huge variety of Cloud services
Posted by Vladimir Yamkovoy on
April 23, 2018
There are three main models of cloud computing, each representing a separate level of providing computing resources, and many other models are much less common, but nevertheless deserving of our attention and your more detailed study, if necessary, to work with these types of services.

(more…)
Cloud ? Cloud … Cloud ! Hybrid Cloud )
Posted by Vladimir Yamkovoy on
April 11, 2018
In recent years, cloud services are becoming more popular. Such infrastructures are today one of the most dynamically developing segments of the IT market, and according to forecasts of specialists around the world, this trend will not only continue in the future but also will grow and more and more people, organizations, representatives of small businesses and large corporations will prefer such decisions are due to the advantage of their application and ease of use.

(more…)
International Backup Day
Posted by Vladimir Yamkovoy on
March 28, 2018
All IT People from around the world on March 31 of each year marks the International Day of Backup.
The backup day was established on the initiative of users of the social news site Reddit and was not randomly appointed on March 31. In the computer environment, there are known cases of information loss on April 1 (these are such “jokes”) – and there is even a whole group of viruses that are activated on that day. The result of their merciless action is a malfunction in the operation of the system or loss of information.
(more…)
Cloud Storages and AcloudA
Posted by Vladimir Yamkovoy on
March 13, 2018
In recent years, more and more popular use of cloud technology. They are used in business processes, web hosting, telecommunications services, in software development and testing, for private use and much more. The main advantage of using cloud technologies and the reason for their ubiquitous distribution is the lack of the need to have a powerful computing system for the end user, which unambiguously leads to a significant cost reduction for business or ordinary end users. In addition, the cloud services provider takes care of the work of the system and applications, provides technical support to users, installs updates on its own and upgrades the computing servers and storage servers. Thus, the user is less concerned with technical issues related to the operation of the system and he can focus on his goals.
As part of the cloud infrastructure, cloud storages can be distinguished.

(more…)
What is the difference between VMware ESXi, vCenter vSphere?
Posted by Vladimir Yamkovoy on
February 26, 2018
When in the distant 2001 the VMware ESXi hypervisor appeared on the market, a virtual revolution started that began the end of the era of personal computers with the programs installed on them. This event opened a new era in the development of computers and software – client-server technologies and cloud computing technologies.
(more…)
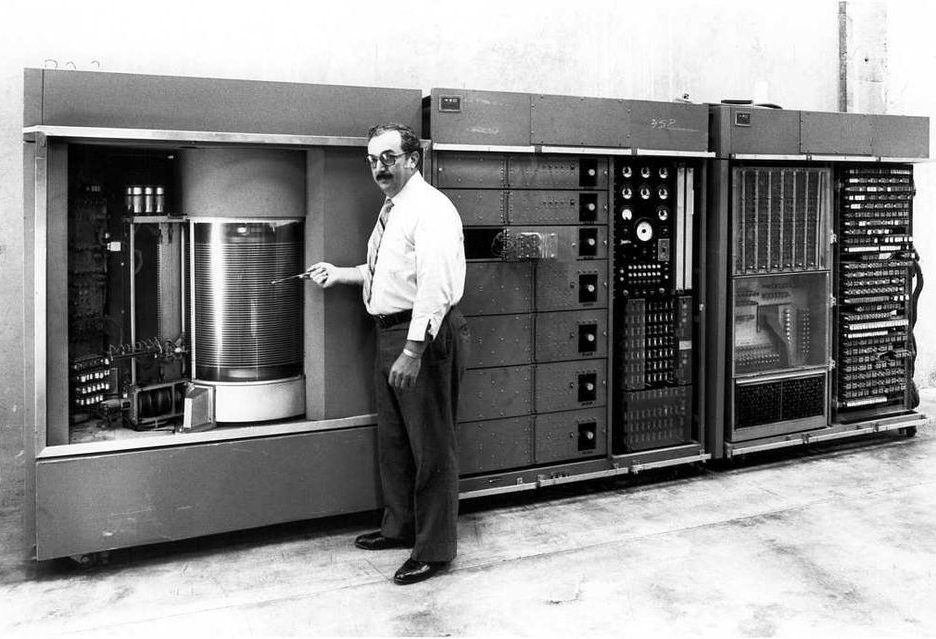
From an HDD the size of a cabinet to a modern SSD in 2.5” size!
Posted by Vladimir Yamkovoy on
February 13, 2018
In 1956, IBM introduced a product that marked the beginning of the computer industry. And the name of this device is HDD.
(more…)